In an X post on May 5, Kelp DAO confirmed that it is migrating its rsETH liquid restaking token away from LayerZero’s OFT standard to Chainlink’s CCIP, citing the April 18 exploit that drained $292 million. With the announcement, Kelp DAO also published screenshots of communications with LayerZero personnel showing the company’s team approved the 1-of-1 verifier setup responsible for the loss.
The migration is already technically underway. Kelp’s GitHub repository now lists “CCIP (Chainlink) RSETH (New)” alongside the legacy LayerZero RSETH_OFT contract.

Kelp says LayerZero approved the setup it later blamed
The April 18 attack on Kelp DAO drained 116,500 rsETH, about 18% of the liquid restaked token (LRT) in circulation from its LayerZero-powered bridge. According to Chainalysis, the attackers compromised internal RPC nodes operated by LayerZero Labs and used a DDoS attack to force traffic onto the poisoned nodes.
The 1-of-1 Decentralized Verifier Network configuration meant a single forged signature was enough for the destination chain to release tokens with no matching burn upstream.
LayerZero’s April 19 post-mortem said Kelp’s setup “directly contradicts” the multi-DVN model LayerZero recommends. Kelp’s May 5 response disputes that characterization.
After the recent LayerZero exploit, we are taking steps to ensure rsETH is fully secure, which is why we are migrating to @chainlink CCIP.
From the April 18 incident, it is clear that LayerZero’s own infrastructure was exploited, resulting in $300M in losses across DeFi.… https://t.co/beIrfZZLlh
— Kelp (@KelpDAO) May 5, 2026
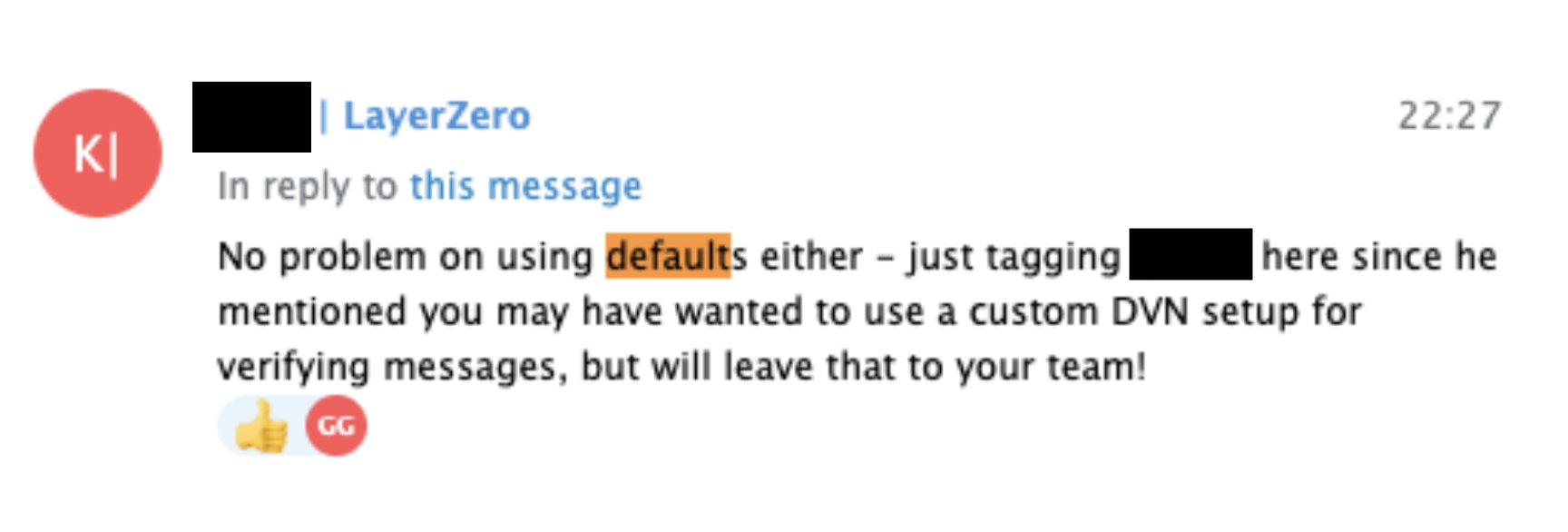
One screenshot Kelp published quotes a LayerZero team member writing: “No problem on using defaults either.” The exchange dates from Kelp’s L2 expansion and references the same 1-of-1 LayerZero Labs DVN configuration later cited in the post-mortem.
The data backs Kelp’s position on how widespread the configuration was. Reports suggest that 47% of active LayerZero OApp contracts used a 1-of-1 DVN setup at the time of the exploit. LayerZero has since banned the complicit configuration and is pushing a migration for every affected application.
The same default appeared in LayerZero’s own V2 OApp Quickstart and bug bounty scope, which excluded application-level verifier choices from rewards.
As Cryptopolitan reported in late April, the exploit triggered Aave TVL outflows of $13 billion within days, with bad debt exposure at the lending protocol estimated at $177 million before recovery efforts began.
Why Kelp DAO chose Chainlink CCIP
According to Chainlink co-founder Sergey Nazarov, CCIP’s architecture differs from bridge alternatives in three structural ways:
- Each lane on CCIP runs three separate Oracle networks rather than three nodes inside one network. Each network is responsible for confirming a different aspect of the transaction. So, compromising one does not affect the other.
- A separate risk management network sits alongside the core protocol, where teams can encode chain-specific policies, such as rules for handling reorgs or new attack vectors, without changing the underlying code.
- The risk management network and transaction networks were built by different teams in different programming languages. A flaw in one codebase does not extend to the other.
In essence, CCIP reduces the chance that one compromised verification path can authorize a bad rsETH release.
Even if you’re able to break one of those codebases because you know one language or you found one flaw, that flaw does not extend to the other codebase.
– Sergey Nazarov.
“It’s really the only bridge in which you have a kind of client diversity and separate codebases interacting with each other in a secure way,” he added.
The April 18 exploit succeeded because there was one verifier, one set of code, and one infrastructure operator to compromise.
CCIP has been operating without a publicly disclosed value-loss incident since launch.
What comes next
LayerZero pledged 10,000 ETH to the DeFi United recovery fund last week. Arbitrum’s Security Council froze 30,766 ETH from the attacker’s wallets.
The legal status of those funds remains contested after US claimants with terrorism-related judgments against North Korea moved to attach them as DPRK property earlier this month.
For Kelp, the migration to CCIP is the structural answer. For LayerZero, the forced multi-DVN migration across roughly half its application base is what comes after the worst DeFi exploit of 2026 so far.
Your bank is using your money. You’re getting the scraps. Watch our free video on becoming your own bank











